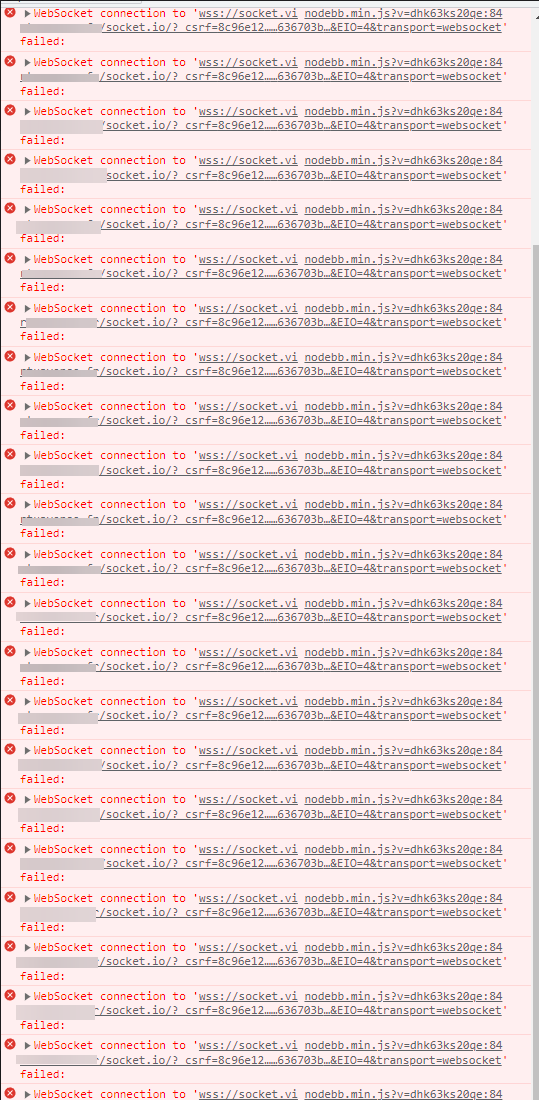
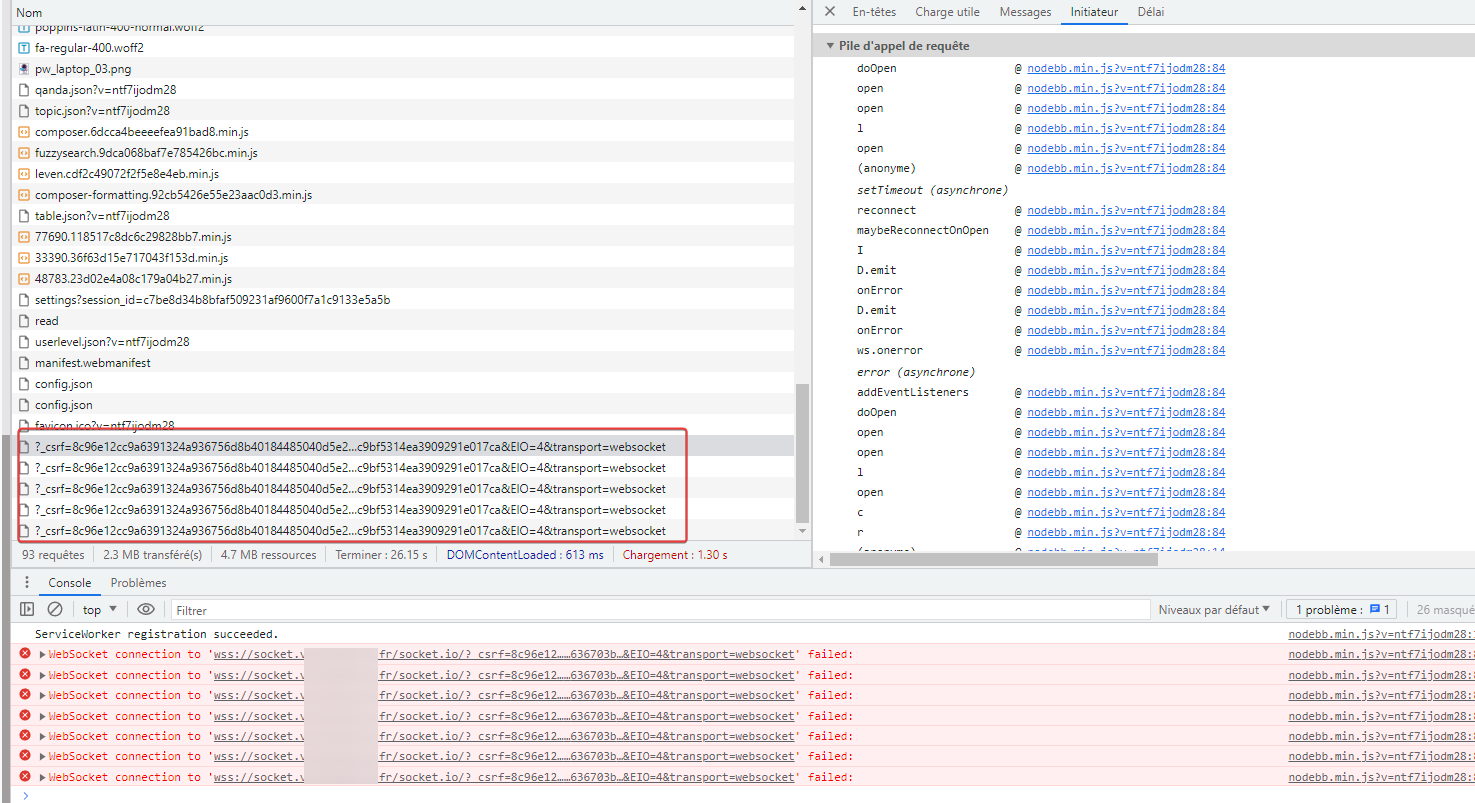
@DownPW said in NodeBB socket with CloudFlare:
one of CloudFlare’s features of hiding the origin server’s IP is THE feature that makes me not really want to leave CloudFlare unless there’s another way to do it ?
No, there isn’t. The way Cloudflare works is to force all of the traffic through a reverse proxy which they control - so even if your request originates in France, it’s going to the US first to be spooled through Cloudflare’s proxy service before being sent onto the origin server.
This has two undesired results
- Traffic eavesdropping by Cloudflare
- Sending traffic through a US entity meaning privacy is not going to be respected, or even if it is, it will me much less than you desire and you cannot change that
Legacy tools such as cloudfail.py could easily bypass the reverse proxy and expose the origin address. These days, that tool only works on seriously weak configurations, but ZenRows will still work and can easily expose the IP you are attempting to hide.
https://www.zenrows.com/blog/cloudfail
You could set up a VPS with a reverse proxy to send the requests onto the origin, so you would only be exposing the reverse proxy itself in the same manner as Cloudflare, but that adds an additional hop, and also presents a single point of failure and something else to monitor and check.
@DownPW said in NodeBB socket with CloudFlare:
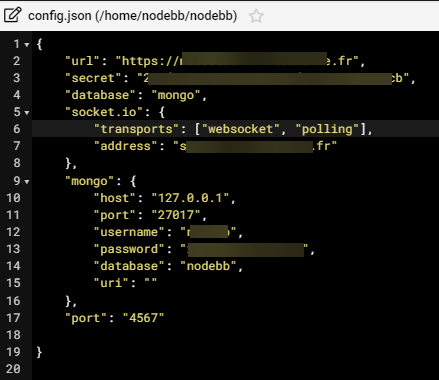
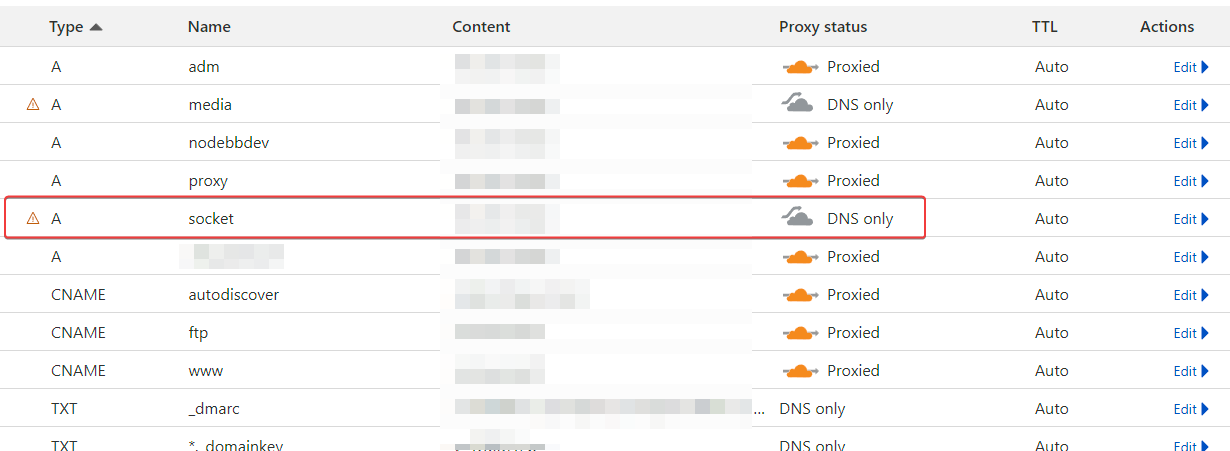
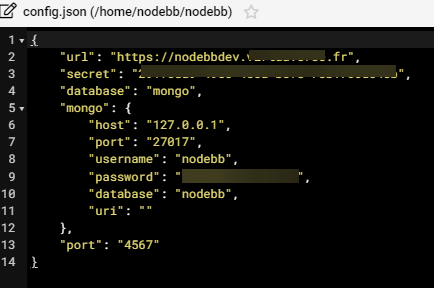
That said, the problem being mainly the socket connections, wouldn’t it be possible to pass ONLY its connections without going through CloudFlare? To do this, you will have to create a subdomain of the root domain and not proxy it via Cloudflare but just in DNS Only, then indicate this in nodebb’s config.json
That’s possible, but you would then need to route socket.io through a sub domain in DNS mode only. This is pointless in terms of protection, as the sub domain could then be used to expose the origin host, and you’ve gained nothing.
@DownPW said in NodeBB socket with CloudFlare:
If I’m not mistaken, this might fix the wss and error 400 issues.
Correct, but the above point still remains
@DownPW said in NodeBB socket with CloudFlare:
This would solve a lot of problem with CloudFlare’s free plan no?
Not really. You still have the Bot Fight Mode issue where the enhanced protection means your site cannot be crawled by Google for example, as their entire ASN will be blocked.
@DownPW said in NodeBB socket with CloudFlare:
Afterwards I am ready to leave CloudFlare if another possibility of hiding your IP is possible but in the meantime, could this be a solution ?
I don’t understand why people insist on hiding behind Cloudflare.
- Going through the proxy service at Cloudflare will slow your traffic down. Think of a funnel - it’s wide at the top, and very narrow at the bottom to fit into the available space (such as the neck of a bottle). Traffic arriving here starts out with having say 8 lanes to enter, then goes down to 1 with severe congestion meaning everything else has to wait behind what’s in front.
Effectively, something like this 

The free plan is first come, first served meaning there is no guarantees of traffic being delivered, meaning that anything time sensitive will suffer as a result. This is that causes socket.io to respond with http 400 because the connection is not established in time.
If you think about how TCP works, then in a lot of cases, the delay is not noticeable as most TCP requests will wait for 30 seconds before being terminated (whereas in direct contrast, UDP will request a connection and not wait for a response). Sockets however are different as they provide a direct connection to the origin, and can be re-used to send traffic back and forth without needing to establish a new connection every time. However, if a remote socket does not receive a response in a set period of time, that session is closed and a new one needs to be opened.
This is a security mechanism to prevent the socket from being exploited and providing a direct route to the origin host.
Hiding your IP address is security through obscurity, and generally, bad practice
https://www.777networks.co.uk/what-is-security-through-obscurity-and-why-is-it-bad/
Hiding behind Cloudflare with no other protection in place is an effective air-gap, but once you circumvent the proxy IP (which is definitely possible), you are a sitting duck if you’ve relied on CF to protect you.