administrators
Posts
-
AI... A new dawn, or the demise of humanity ? -
AI... A new dawn, or the demise of humanity ?@crazycells Agree. The distribution of Revenge Porn is already illegal, so why is this not? it’s technically along the same lines?
-
AI... A new dawn, or the demise of humanity ?@phenomlab said in AI... A new dawn, or the demise of humanity ?:
Seems this specific issue is becoming more widespread
-
AI... A new dawn, or the demise of humanity ?Interesting. London has been identified as a huge talent pool for AI by Microsoft.
-
AI... A new dawn, or the demise of humanity ? -
Extended functions for Q&A NodeBB pluginI wanted to add functionality into Sudonix so that it
a) Adds a new DIV in the form of a panel/card after the last post if the topic is “solved”
b) Adds a link that will take you straight to the solution
c) Scrolls to that particular DIV containing the solution using page scrolling with an offsetBasically, it would look like this - see video below:
To my mind, this is a nice touch - a key feature that is missing from the Q&A plugin. I’ve asked for it to be added, although I’m not sure how much of an appetite there is for this, so with some simple HTML, NodeBB Widget areas, and some jQuery, it’s all possible

Widget code below:
https://github.com/phenomlab/nodebb-q-a-extension/blob/main/widget.html
How to use
- Open
/admin/extend/widgets - Drag and drop a HTML widget into the
topic.tpltemplate, positioned in the Topic Footer - Paste the code from Github into the HTML pane like below
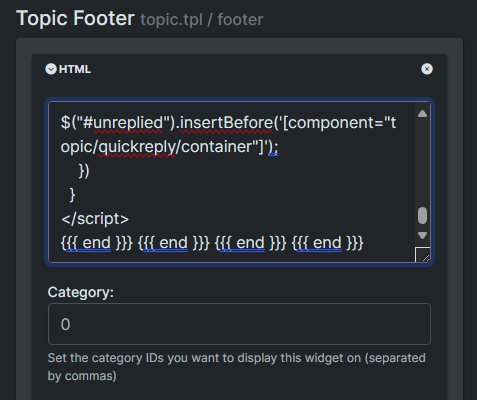
- Save the changes
Add this into your custom CSS
/admin/appearance/customise#custom-css. Note that this is a “starting point” that usesvarand so you will need to adjust to fir your own site.https://github.com/phenomlab/nodebb-q-a-extension/blob/main/style.css
From now, any topics which are enabled for Q&A and set to a question will look something like the below
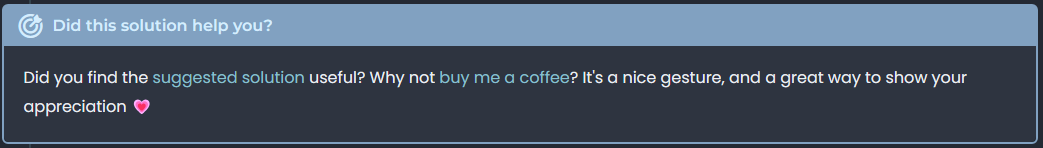
Resolved
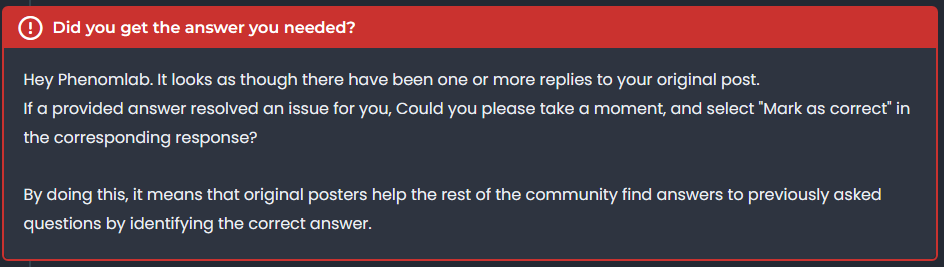
Unresolved
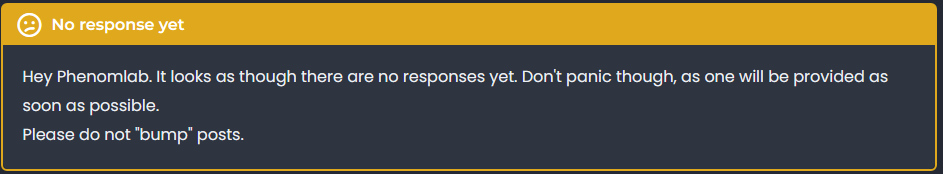
Unanswered
This makes the Q&A plugin a bit more intuitive - what do you think?
- Open
-
Page control arrows for PWA@crazycells it is, yes - I think I’ll leave it as there is no specific PWA CSS classes I know of. Well, you could use something like the below, but this means multiple CSS files for different operating systems.
/** * Determine the mobile operating system. * This function returns one of 'iOS', 'Android', 'Windows Phone', or 'unknown'. * * @returns {String} */ function getMobileOperatingSystem() { var userAgent = navigator.userAgent || navigator.vendor || window.opera; // Windows Phone must come first because its UA also contains "Android" if (/windows phone/i.test(userAgent)) { return "Windows Phone"; } if (/android/i.test(userAgent)) { return "Android"; } if (/iPad|iPhone|iPod/.test(userAgent) && !window.MSStream) { return "iOS"; } return "unknown"; // return “Android” - one should either handle the unknown or fallback to a specific platform, let’s say Android }Once you’re in that rabbit hole, it’s impossible to get out of it.
-
Page control arrows for PWA@crazycells Good point, thanks.
-
Page control arrows for PWA@crazycells Ok, but there’s no “scroll-down”
