
ProtonMail often touts its Swiss jurisdiction and privacy guarantees, but at the same time, it is complying with a record number of data request orders going through the Swiss legal system.
ProtonMail is one of the most popular secure email services in the world, having launched in 2014 via a crowdfunding campaign. It promises a higher level of privacy and security over other email platforms and frequently touts its Swiss jurisdiction.
While Switzerland is a good jurisdiction for privacy-conscious users, it’s certainly no guarantee for data security.
On the ProtonMail homepage, you can see references to “strict Swiss privacy laws” that should keep your data secure.
Proton provides data to the FBI and other police agencies
This past week Forbes ran an article on a case where the FBI was able to get data on a U.S. ProtonMail user who was being investigated for harassment (but not charged with any crime).
The warrant revealed that the FBI managed to acquire data from Proton Technologies, the owner of Proton Mail, to kick off the hunt for the anonymous emailer. It’s a rare example of a U.S. data request on Proton and shows how small pieces of metadata from encrypted software can prove hugely useful for cops trying to unmask users who expect strong privacy protections from such apps.
– Forbes
In this case, Proton Technologies provided the FBI with the “recovery and associated email addresses” of the user, which lead to his discovery.
Two years ago, RestorePrivacy ran an article on another ProtonMail logging case involving a French activist who was also a ProtonMail user. In that case, French police received the user’s IP address from Proton Technologies, leading to the arrest of the suspect.
This begs the question, how common are cases like these, particularly with cases that don’t end up in the news?
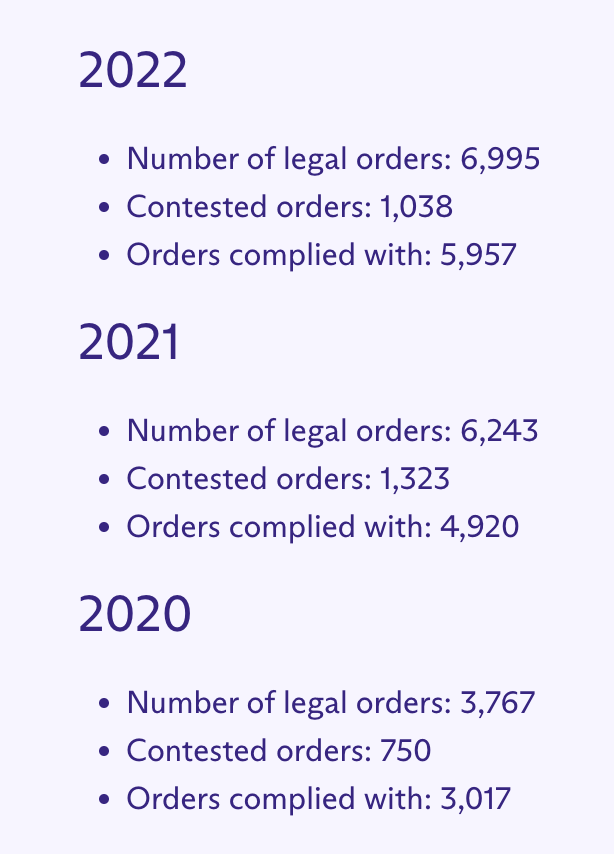
Nearly 6,000 data request orders “complied with” in 2022
To ProtonMail’s credit, the organization publishes a transparency report going back to 2017. In it, we find the following statistics detailing legal orders for user data.
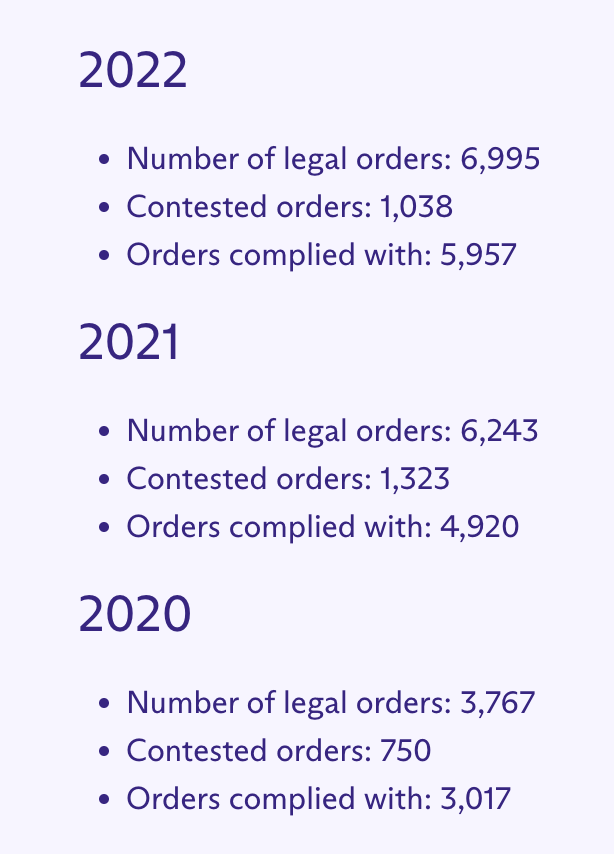
Additionally, you can see that the number for all three categories continues to climb every year. With that being said, this growth is also not surprising given that ProtonMail is a popular brand with a growing user base. Aside from email, the company also offers Proton VPN and a Proton Pass, a password manager.
Proton prefaces the transparency report noting that data requests must go through Swiss legal channels.
From time to time, Proton may be legally compelled to disclose certain user information to Swiss authorities, as detailed in our Privacy Policy. This can happen if Swiss law is broken.
… Swiss authorities may from time to time assist foreign authorities with requests, provided that they are valid under international legal assistance procedures and determined to be in compliance with Swiss law. In these cases, the standard of legality is again based on Swiss law.
– Proton Transparency Report
Proton Mail provided us with an explanation for the growing number of cases below.
The increase in cases reflects the increase in our user base. As Proton has scaled, and now has 100m sign ups to our services, it’s not surprising that these figures have risen. However, these cases have come through the Swiss authorities (which is a good sense check of their validity) and have also been reviewed by Proton to ensure they are reasonable for us to respond to (hence why there are also cases that we have not complied with mentioned on the transparency report). Please note that in all cases email content, attachments, files etc are always encrypted and cannot be read.
– Proton spokesperson
Is Proton Mail still secure and private?
The answer to this question all boils down to determining your threat model and the adversaries you are trying to protect yourself against.
In short, the answer is yes if you are looking for a secure, encrypted email service that does not have access to the contents of your inbox. After all, ProtonMail is far better than Gmail or Yahoo when it comes to privacy.
If you are doing things to attract the attention of law enforcement, then the data you provide when you use ProtonMail, such as IP address and recovery email, may be shared with authorities if Proton Technologies is legally compelled to do so in Swiss court.
All businesses must comply with the laws in the countries where they are legally based. The only other option is to shut down, like we saw with CTemplar in 2022 and Lavabit back in 2013.
Furthermore, there are also different alternatives with various privacy and security benefits, as you can see in our secure email guide.
Consider your OPSEC
It’s also important to consider what data you provide when you sign up for a service. In the ProtonMail cases we mentioned above, the data that exposed the users was the user’s IP address (French activist) and the “recovery and associated email addresses” (US suspect investigated by the FBI recently).
By protecting the data you provide when interacting with the email service, you can make your email account even more private and secure.
- IP address – Use a good VPN service to hide your IP address whenever using the email service (or anytime you are online for that matter)
- Recovery email – Consider using a disposable email for a recovery email, or a new and unused recovery email address that is not linked to your identity
- Payment methods – Email is fundamentally different from a no logs VPN service in that there is always personal data stored (your inbox contents and other account data). Therefore it’s more important to use an anonymous payment method if you want more privacy.
Having good OPSEC is a crucial consideration whenever you are using privacy tools.
– Source :
https://restoreprivacy.com/protonmail-data-requests-user-logs/


 but I am asking from the server security perspective. Do you think someone could enter Gmail servers or Proton servers more easily?
but I am asking from the server security perspective. Do you think someone could enter Gmail servers or Proton servers more easily?