@sebmegag hi. Welcome aboard! I’ve tried this on both iPhone and Android and it works fine. Did you double check the config you have?
How to install a self-hosted instance of iFramely for use with NodeBB
-
Thanks @crazycells for your code, I will test it, for sure

@phenomlab Resources level, do you know to what extent the CPU will be impacted by Iframely?
Generally speaking, our forum uses between 20 and 50% of the CPU. With peaks at 80-90 which return an excess load and unavailability to the forum (a few seconds).
-
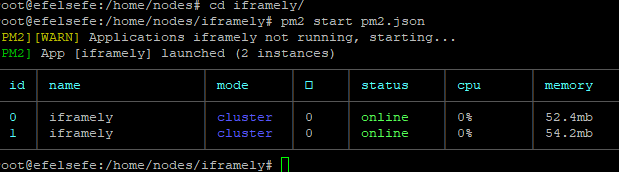
@DownPW iFramely is multi threaded and runs as a cluster, so will spread itself across the amount of cores you have. If you run
pm2 statusyou’ll see how many cores it’s using, plus the memory usage.I’ve never had an issue with it and I know that thousands of sites have it installed with no performance degradation. It scales very well and only seems to occupy a small selection of CPU and memory.
-
Ok @phenomlab
Thanks for your answer but with pm2 status command, I see a % of CPU used but not the number of CPU core used…
-
@DownPW how many cores do you have ?
-
-
@DownPW OMG

-
ha ha, i’m tired voila

you say this:
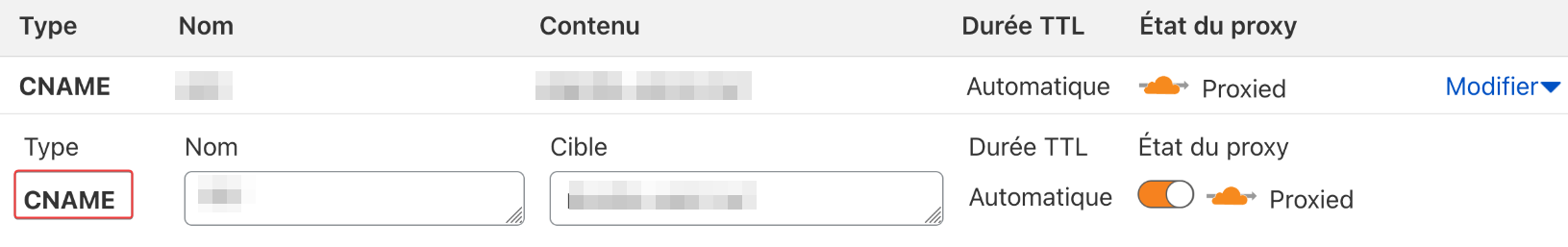
if you are using Cloudflare, this particular port (8061) isn’t routable with the free plan, so something to be aware of
@phenomlab
I’m using a free plan from CloudFlare, will this bother me for use Iframely on my server? -
@DownPW only if you choose to not proxy the traffic (grey cloud only, which is just DNS rather than the default orange cloud)
-
@DownPW you will win this war

-
-
@DownPW no. It needs to be an A record. CNAME is canonical meaning that traffic sent to it will land up at your main nginx site. The A record will sent headers which nginx can use to route the traffic correctly.
CNAME records do not have this and will resolve to the underlying host which will cause you problems. Useful for WWW and non-WWW, but that’s about it.
Essentially, it’s an alias and not a record in it’s own right.
-
@phenomlab i think my ifamely started to not work i dont know why
 youtube embed not working
youtube embed not working 

[PM2][ERROR] Process or Namespace iframely not found
[PM2][WARN] Current process list is not synchronized with saved list. App iframely iframely differs. Type ‘pm2 save’ to synchronize. -
@cagatay is the
iframelyservice started ? That error message would indicate it’s not running -
@phenomlab as a result of ps -x i cant see iframely service pid id so i think its not working automaticly when i rebooted the server. How can i start it?
-
@cagatay try
pm2 start pm2.jsonwhich needs to be executed from the directory of the iFramely domain where it is installed. See previous documentation I provided after the installation.A quicker route would be to reboot your VPS to see if that resolves the issue.
-
hope everything is ok from now.
-
@phenomlab when i reboot the vps nodebb and iframely not working auto

but manually everything is working fine right now. -
@cagatay ok, that needs looking at then as it seems it’s not configured properly. For now of course you can start it manually.
-
Hello @phenomlab
I like your iframe :
Can you please provide your CSS code with me for Iframely Iframe ?
Thanks in advance dude
-
@DownPW this was actually stolen from @crazycells (
 ) and slightly modified, so I can’t really take the credit.
) and slightly modified, so I can’t really take the credit.His original response to the iFramely guide I posted contains the CSS he’s using is here
-
 undefined phenomlab referenced this topic on
undefined phenomlab referenced this topic on
-
-
NodeBB: Consent page
Solved Configure -
-
-
-
-
iFramely self host help
Solved Configure -