@DownPW any update?
Issues getting Flarum to work on new host
-
@Hari You create this in Virtualmin
https://archive.virtualmin.com/comment/715598#comment-715598
-
Failed to save user : SQL drop user if exists 'asku@ask.domain.com'@'localhost' failed : String 'asku@ask.domain.com' is too long for user name (should be no longer than 32)looks like my domain name is too big, never thought this will be an a issue
 how to handle this?
how to handle this? -
@Hari Looks like you are attempting to rename the existing user ? I wouldn’t do that.
Login to MySQL as root, and run
show create table mysql.userWhat’s the output of that command ?
-
localhost/ https://ip/phpmyadmin/index.php?route=/server/sql Your SQL query has been executed successfully. show create table mysql.user; user CREATE TABLE `user` ( `Host` char(255) CHARACTER...as root i could not able to grant permission to a user

-
@Hari This doesn’t look right to me. Can you PM the server details plus a username and password I can use to access and take a look ?
-
@phenomlab sure, i have deleted that user and created a new DB and user “askDO” shared logins via PM
lol, meanwhile i am trying to install composer

root@ask public_html]# composer require blomastra/flarum-redis:* sh: 1: composer: not found [root@ask public_html]# mv composer.phar /usr/local/bin/composer mv: cannot stat 'composer.phar': No such file or directory [root@ask public_html]# php composer-setup.php --install-dir=bin --filename=composer Could not open input file: composer-setup.php [root@ask public_html]# php composer-setup.php --install-dir=bin --filename=composer Could not open input file: composer-setup.php [root@ask public_html]# -
@Hari said in how can i create a mysql user in virtualmin:
sure, i have deleted that user and created a new DB and user “askDO” shared logins via PM
Everything looks to be in order. The user
askDOseems to have full access to that database. Is this now working ? -
@phenomlab i have changed the domain in flarum config file to IP but it is not working, trying to install composer now
-
@Hari checking
-
@Hari It’s looking for a Redis install. Is this active ?
[2022-02-16 11:57:15] flarum.ERROR: Predis\Connection\ConnectionException: Connection refused [tcp://127.0.0.1:6379] -
@phenomlab yes, after installing composer i am supposed to install redis
-
@Hari Did you install composer as per this guide ?
https://getcomposer.org/download/
Essentially, it’s this
php -r "copy('https://getcomposer.org/installer', 'composer-setup.php');" php -r "if (hash_file('sha384', 'composer-setup.php') === '906a84df04cea2aa72f40b5f787e49f22d4c2f19492ac310e8cba5b96ac8b64115ac402c8cd292b8a03482574915d1a8') { echo 'Installer verified'; } else { echo 'Installer corrupt'; unlink('composer-setup.php'); } echo PHP_EOL;" php composer-setup.php php -r "unlink('composer-setup.php');" -
@phenomlab yes,

-
@Hari It’s not installed
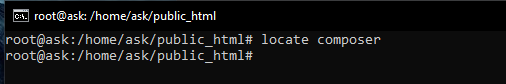
EDIT: Seems it is installed, but not correctly. You should be able to run this simply as
composer. However,php composer.pharwill work, but it’s clumsy to type… -
i followed these two guides
php composer.phar
https://getcomposer.org/download/
https://getcomposer.org/doc/00-intro.mdi think i installed it in multiple places root and public_html
how can i fix it?
-
@Hari Ok. Let me have a look at this for you.
-
@Hari done. You should now be able to run
composerdirectly as any user (preferably not root) inside thepublic_htmldirectory.Essentially, it needs to be installed as
php composer-setup.php --install-dir=/usr/bin --filename=composer -
@phenomlab sir, do i need to move any files now? or did you fix it ?
-
@Hari Fixed. No need to move anything. It should just “work”

-
@Hari you can go ahead and use
sudo apt install redis-server redis-toolsto get Redis up and running now. After that, (hopefully) Flarum should boot.
Did this solution help you?
-
-
-
-
-
-
-
-
SASL LOGIN authentication failed: generic failure
Moved Solved Linux