@DownPW here. Hostrisk is automated and doesn’t accept registrations.
Hackers aren't evil - separating fact and FUD
-

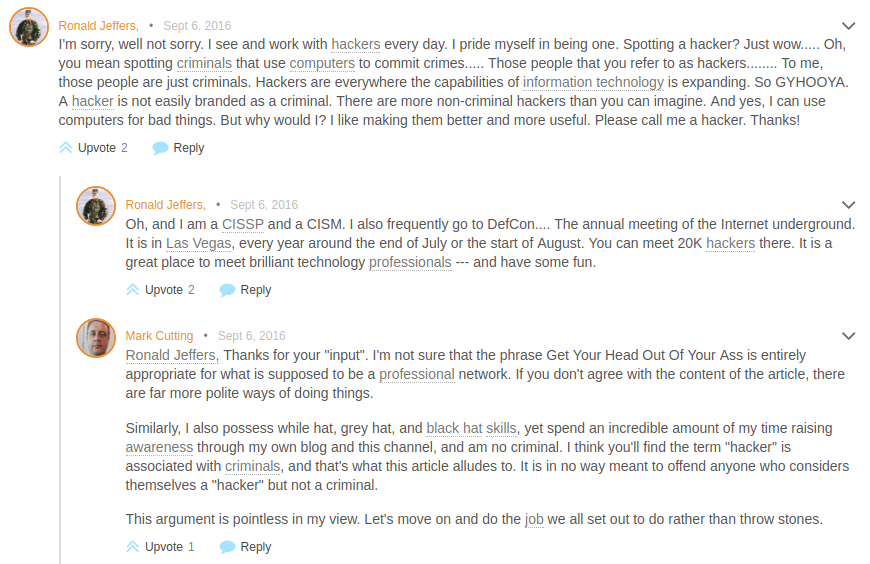
One of many issues with working in the Infosec community is an inevitable backlash you’ll come across almost on a daily basis. In this industry, and probably hundreds of others like it are those who have an opinion. There’s absolutely nothing wrong with that, and it’s something I always actively encourage. However, there’s a fine line between what is considered to be constructive opinion and what comes across as a bigoted approach. What I’m alluding to here is the usage of the word “hacker” and it’s context. I’ve written about this particular topic before which, so it seems, appears to have pressed a few buttons that “shouldn’t be pressed”.
But why is this ?
The purpose of this article is definition. It really isn’t designed to “take sides” or cast aspersions over the correct usage of the term, or which scenarios and paradigms it is used correctly or incorrectly against. For the most part, the term “hacker” seems to be seen as positive in the Infosec community, and based on this, the general consensus is that there should be greater awareness of the differences between hackers and threat actors, for example. The issue here is that not everyone outside of this arena is inclined to agree. You could argue that the root of this issue is mainly attributed to the media and how they portray “hackers” as individuals who pursue nefarious activity and use their skills to commit crime and theft on a grand scale by gaining illegal access to networks. On the one hand, the image of hoodies and faceless individuals has created a positive awareness and a sense of caution amongst the target groups – these being everyday users of civilian systems and corporate networks alike, and with the constant stream of awareness campaigns running on a daily basis, this paradigm serves only to perpetuate rather than diminish. On the other hand, if you research the definition of the term “hacker” you’ll find more than one returned.
Is this a fair reflection of hackers ? To the untrained eye, picture number 2 probably creates the most excitement. Sure, picture 1 looks “cool”, but it’s not “threatening” as such, as this is clearly the image the media wants to display. Essentially, they have probably taken this stance to increase awareness of an anonymous and faceless threat. But, it ISN’T a fair portrayal.
Current definitions of “the word”
The word “hacker” has become synonymous with criminal activity to the point where it cannot be reversed. Certainly not overnight anyway. The media attention cannot be directly blamed either in my view as without these types of campaigns, the impact of such a threat wouldn’t be taken seriously if a picture of a guy in a suit (state sponsored) was used. The hoodie is representative of an unknown masked assailant and it’s creation is for awareness – to those who have no real understanding of what a hacker should look like – hence my original article. As I highlighted above, we live in a world where a picture speaks a thousand words.
The word hacker is always going to be associated with nefarious activity and that’s never going to change, regardless of the amount of effort that would be needed to re-educate pretty much the entire planet. Ask anyone to define a hacker and you’ll get the same response. It’s almost like trying to distinguish the deference between a full blown criminal and a “lovable rogue” or the fact that hoodies aren’t trouble making adolescent thugs.
Ultimately, it’s far too ingrained – much like the letters that flow through a stick of rock found on UK seaside resorts. It’s doesn’t matter how much you break off, the lettering exists throughout the entire stick regardless if you want that to happen or not. To make a real change, and most importantly, have media (and by definition, everyone else) realise they have made a fundamental misjudgement, we should look at realistic definitions.
The most notable is the below, taken from Tech Target
A hacker is an individual who uses computer, networking or other skills to overcome a technical problem. The term hacker may refer to anyone with technical skills, but it often refers to a person who uses his or her abilities to gain unauthorized access to systems or networks in order to commit crimes. A hacker may, for example, steal information to hurt people via identity theft, damage or bring down systems and, often, hold those systems hostage to collect ransom.
The term hacker has historically been a divisive one, sometimes being used as a term of admiration for an individual who exhibits a high degree of skill, as well as creativity in his or her approach to technical problems. However, the term is more commonly applied to an individual who uses this skill for illegal or unethical purposes.
One great example of this is that hackers are not “evil people” but are in fact industry professionals and experts who use their knowledge to raise awareness by conducting proof of concept exercises and providing education and awareness around the millions of threats that we are exposed to on an almost daily basis. So why does the word “hacker” strike fear into those unfamiliar with its true meaning ? The reasoning for this unnecessary phenomena isn’t actually the media alone (although they have contributed significantly to it’s popularity). It’s perception. You could argue that the media have made this perception worse, and to a degree, this would be true. However, they actually didn’t create the original alliance – the MIT claimed that trophy and gave the term the “meaning” it has to this day. Have a look at this
Given the origins of this date back to 1963, the media is not to blame for creating the seemingly incorrect original reference when it’s fairly obvious that they didn’t. The “newspaper” reflected in the link is a campus circulation and was never designed for public consumption as far as I can see. Here’s a quote from that article:
“Many telephone services have been curtailed because of so-called hackers, according to Professor Carleton Tucker, administrator of the Institute telephone system.
The students have accomplished such things as tying up all the tie-lines between Harvard and MIT, or making long-distance calls by charging them to a local radar installation. One method involved connecting the PDP-1 computer to the phone system to search the lines until a dial tone, indicating an outside line, was found.”
The “so-called hackers” alignment here originally comes from “Phreaking” – a traditional method of establishing control over remote telephone systems allowing trunk calls, international dialling, premium rates, etc, all without the administrator’s knowledge. This “old school” method would certainly no longer work with modern phone systems, but is certainly “up there” with the established activity that draws a parallel with hacking.
Whilst a significant portion of blogs, security forums, and even professional security platforms continue to use images of hoodies, faceless individuals, and the term “hacker” in the criminal sense, this is clearly a misconception – unfortunately one that connotation itself has allowed to set in stone like King Arthur’s Excalibur. In fairness, cyber criminals are mostly faceless individuals as nobody can actually see them commit a crime and only realise they are in fact normal people once they are discovered, arrested, and brought to trial for their activities. However, the term “hacker” is being misused on a grand scale – and has been since the 1980’s.
An interesting observation here is that hoodies are intrinsically linked to threatening behaviour. A classic example of this is here. This really isn’t misrepresentation by the media in this case – it’s an unfortunate reality that is on the increase. Quite who exactly is responsible for putting a hacker in a hoodie is something of a discussion topic, but hackers were originally seen as “Cyberpunks” (think Matrix 1) until the media stepped in where they suddenly were seen as skateboarding kids in hoodies. And so, the image we know (and hackers loathe) was born. Perhaps one “logical” perspective for hoodies and hackers could be the anonymity the hoodie supposedly affords.
The misconception of the true meaning of “hacker” has damaged the Infosec community extensively in terms of what should be a “no chalk” line between what is criminal, and what isn’t. However, it’s not all bad news. True meaning aside, the level of awareness around the nefarious activities of cyber criminals has certainly increased, but until we are able to establish a clear demarcation between ethics in terms of what is right and wrong, those hackers who provide services, education, and awareness will always be painted in a negative light, and by inference, be “tarred with the same brush”. Those who pride themselves on being hackers should continue to do so in my view – and they have my full support.
It’s not their job solely to convince everyone else of their true intent, but ours as a community.
Let’s start making that change.
